.svg)

MACHINE SPEED ATTACK EMULATION
& EDGE DEFENSE
Outside in Red Team simulation, risk exposure and Automatic Remediation
Vulnerability Detection
Mandate
Verified Vulnerabilities
Discovery and threats
Vector Chaining


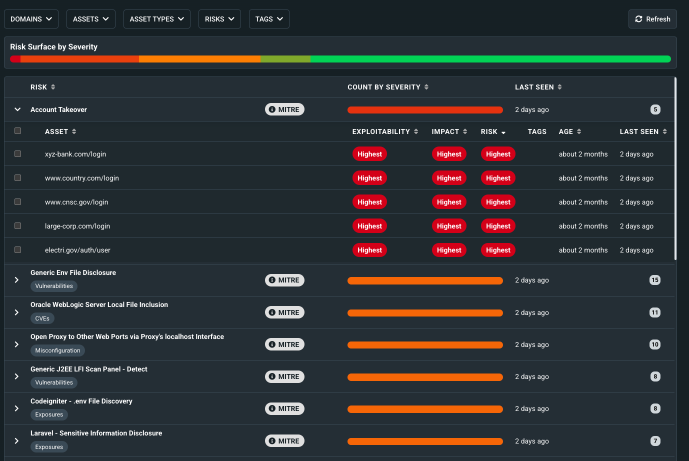

Verifiable Threat Data Features
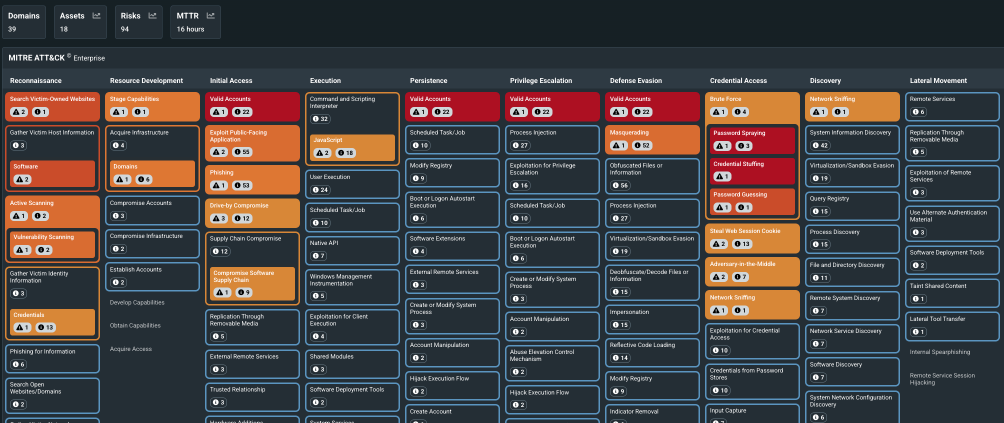
Evidence Based Cybersecurity that maps into your existing ISO 270001, SOC 2, & NIST Cybersecurity Framework
Attack / Breach Simulation
Agentic AI allows for simulation of multi-vector attack types that are often not spotted by traditional means
Clear Reporting and Threat Intel
We show the clear threats, mapped into the relevant Cybersecurity standards.
.svg)
.svg)
Engage with our Team
Schedule your Demo Below
We're committed to your success!
Machine Speed Vulnerability mapping Intel to Verified Threats
VerifiedThreat (VT) transforms raw threat intelligence into active validation. By deploying autonomous, situational AI agents that chain vulnerabilities exactly like a human hacker, VT stress-tests your external attack surface in real-time—safely providing hard empirical proof, erasing false positives, and automatically updating your compliance ledger at the network edge
.svg)
.svg)
Seamless Integration Tools
integration with Major cloud platforms Threat Intel & cyber frameworks / standards
Customer Satisfaction
How We Help Businesses Like Yours Protect.

"Before VerifiedThreat we were constantly putting out fires. As we grew the client base, this just made the problem exponentially worse and was a real barrier to growth. VerifiedThreat helped us protect all our legacy and multi-cloud clients”
" We were getting traffic coming in from large numbers of mobile phones in different locations with all sorts of IP addresses. It was a constant pain that at times was knocking down our APIs". VerifiedThreat was a simple cloud based automated setup that stopped 98% of the problem immediately.
Case Study

"The problem with so many Cybersecurity tools is they just give out more alerts and noise. VerifiedThreat does what is says, and only presents actual threats which are proven. Massive win for me and the team. "
.svg)
.svg)



Frequently asked questions:
How We Help Protect Businesses Like Yours.
Who is your target audience?
We are aimed at medium-to large corporate businesses who need to have verified risk analysis to help prevent attacks. For smaller businesses, this will provide the missing red team intelligence, and in larger companies our massive scale and auto-remediation makes the platform invaluable.
How does it work?
We send out intelligent AI agents to use tiny amounts of data to look for vulnerabilities across your digital estate. These agents are smart and have the situational awareness to leverage one vulnerability and use that to their advantage. Simulating the cyberattacks with real-world methods used by actual hackers allows the agents to spot the weakest link and automatically use the AI tools to prevent the potential attack.
Is this just a fancy pentest?
No! The way VerifiedThreat works is very different from a pen test. VerifiedThreat is Autonomous Threat Emulation. Pentests are heavily reliant on pre-existing threat data , and can't dynamically learn and adapt from their knowledge of your own unique platform. VerifiedThreat monitors continually, and is adaptive. Standard pentesting is very limited in comparison.
Do you integrate with security standards and frameworks ?
We automatically map the verified threats discovered to the relevant cybersecurity standards, so that you see which standards are affected by the risk and how the risk can be addressed and fully mitigated. The risk register is automatically managed.
Who can benefit from VerifiedThreat?
Key stakeholders are the DevOps, CyberSecurity, compliance, and risk management teams.
Blog & News
Stay Up To Date

.svg)








_11zon.webp)

.webp)