Definition of CTEM in Cybersecurity
In cybersecurity, CTEM stands for Continuous Threat Exposure Management and is defined as a framework to help organizations understand and reduce their cyber risk in a continuous, business-aligned manner. Gartner first introduced the CTEM concept in July 2022, in an effort to reduce the gap between the technical exposure vulnerabilities and the actual commercial risk and business priorities. Specifically, CTEM goes beyond the traditional vulnerability management by incorporating real-time assessment, ongoing prioritization, and actionable remediation efforts, and starts to change the focus onto the attacker’s perspective. Major corporations are constantly under some kind of cyberattack - whether they realise it or not. The CTEM framework seeks to fight-fire with fire, by giving them a continuous and proactive cybersecurity framework to move beyond the annual pentest into a continual cycle of assessment, remediation and continuous vigilance.
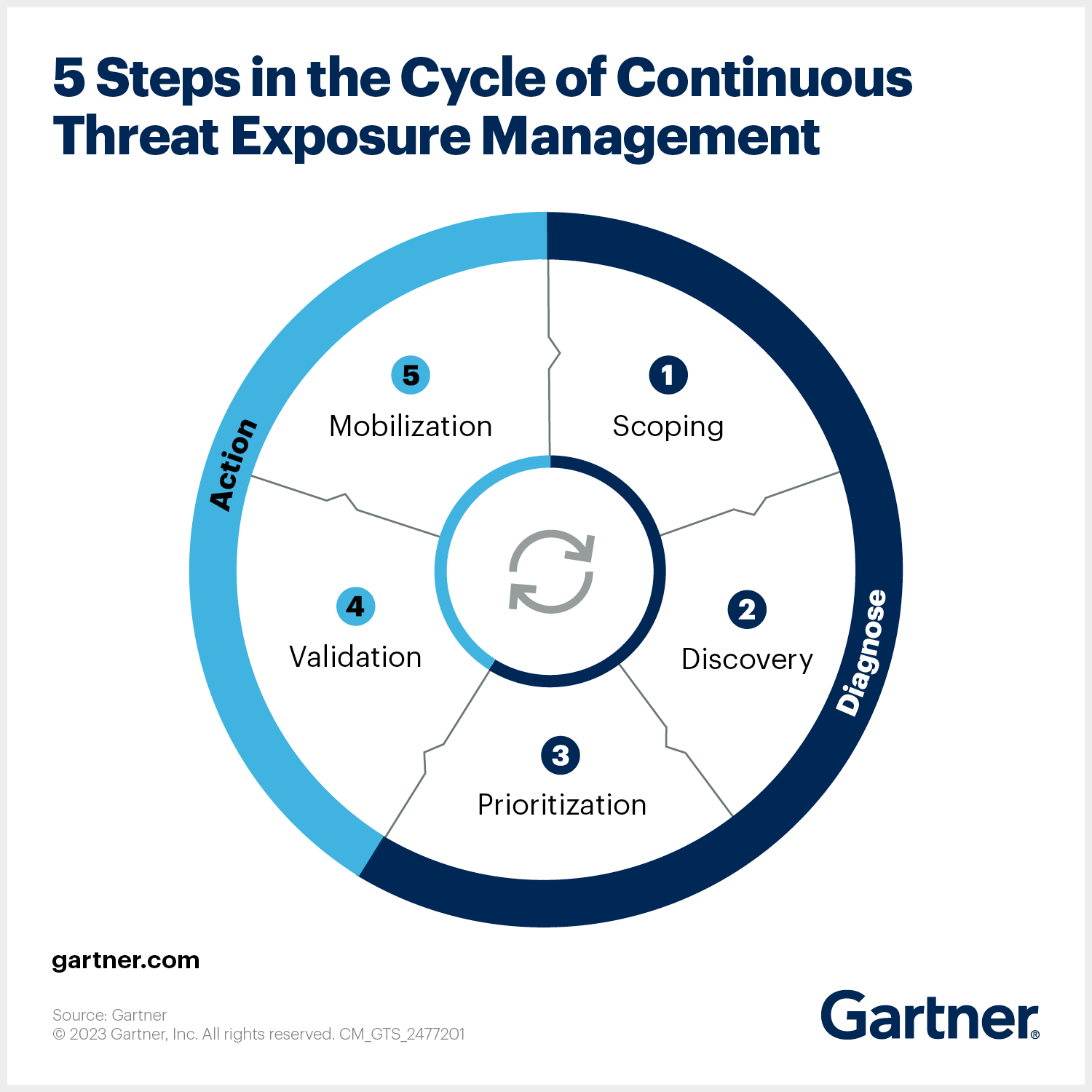
As we can see in the Gartner diagram the CTEM framework uses a cyclical approach of looking through the attackers lens and validates each stage of the scoping, discovery, prioritization, validation, and mobilization phases.
Key Aspects of CTEM
Proactive & Iterative Program: CTEM is not technology as such, but a framework or methodology that moves from periodic to continuously monitors and evaluates an organization's security posture.
The central purpose of CTEM is to ensure that exposures are identified and addressed proactively before adversaries can exploit them. This continuous cycle not only enhances visibility but also helps to strengthen resilience, enabling organizations to transition from reactive defense to proactive protection.
Why do Traditional Approaches Fail?
Cybersecurity threats continue to evolve at an alarming pace, leaving organizations vulnerable to increasingly sophisticated attacks.
Traditional vulnerability management approaches, often based on periodic scanning and remediation cycles, cannot keep up with the rapid changes in the threat landscape.
The traditional vulnerability scanning and periodic pentests would generate a huge amount of reporting data, often based on the purely technical assessments of the risk, which would then have to be validated against the underlying corporate risk appetite and the actual business value of the assets. All of this takes much time and effort, and it’s often difficult to see the wood from the trees, to validate which of the potential threats are a real risk. Many of the vulnerabilities may just not be a real risk to the business, but the traditional vulnerability scanning and pentest would keep on bringing up the same risks over time. Managing the assets discovery, overall risk strategy, and risk validation as well as the overall risk register is often a thankless manual task.
Core Components of a CTEM Framework
A successful CTEM strategy is built on several critical pillars that work together to deliver ongoing risk reduction:
1. Scoping and Asset Identification
The foundation of CTEM begins with defining the scope of monitoring. Organizations must identify which assets, networks, applications, and systems fall within the program. This includes cloud platforms, on-premises infrastructure, IoT devices, APIs, and third-party integrations. This phase is particularly important for understanding the supply chain and third-party infrastructure, as all the various components can be included in the initial scope, to ensure you have a true end-to-end picture of the entire risk.
2. Continuous Discovery
Once scope is established, continuous discovery tools map the attack surface, uncovering vulnerabilities, misconfigurations, and potential weak points. Unlike traditional scans, discovery in CTEM is ongoing and adaptive, providing up-to-date visibility at all times. This is where VerifiedThreat comes into its own. Our agentic AI tools continually scan and use ‘swarm’ techniques to validate and expose potential vulnerabilities using red team attack simulations. This not only helps the discovery process, but continually assesses the risk surface constantly, and helps to reduce false positives and overall noisy data.
3. Prioritization of Exposures
Not all vulnerabilities carry equal weight. One of the big frustrations with traditional vulnerability scanning is the lack of any business prioritisation. VerifiedThreat applies prioritization models that consider not only exploitability, threat intelligence, sector specific threats, but the criticality of affected assets according to the existing risk appetite. By aligning risks with business context, teams focus on exposures that matter most. Combining the reduction in false positives with the increase in business specificity to real risk makes a meaningful impact and overall reduction in false positives by as much as 60-90%.
4. Validation of Threats
CTEM emphasizes validation by simulating attacks to test whether a vulnerability can actually be exploited. This prevents teams from wasting time on theoretical risks and ensures remediation is targeted toward exploitable exposures.
5. Mobilization and Remediation
The final stage of CTEM involves mobilizing resources across IT, security, and operations teams to remediate vulnerabilities. This stage ensures that prioritized exposures are effectively addressed, often leveraging automation for speed and scale.VerifiedThreat’s open API architecture allows the real-time threat data, risk ledger and asset discovery data to be easily consumed and shared across the enterprise as a feed.
Why CTEM is Essential for Modern Cybersecurity
Proactive Defense Against Advanced Threats
Cyber adversaries exploit vulnerabilities within hours of disclosure. CTEM closes the gap by identifying and prioritizing risks before attackers can leverage them.
Alignment with Business Objectives
Unlike traditional approaches, CTEM integrates business impact into prioritization, ensuring that remediation efforts are aligned with organizational goals and risk appetite.
Enhanced Regulatory Compliance
Continuous monitoring supports compliance with frameworks such as ISO 27001, PCI-DSS, GDPR, SOC 2, and NIST by demonstrating proactive risk management.
Improved Incident Readiness
With validated exposures and real-time intelligence, incident response teams are better prepared to prevent and contain breaches quickly.
Benefits of Implementing CTEM
- Continuous Attack Surface Visibility – Real-time understanding of vulnerabilities across cloud, hybrid, and on-premises systems.
- Reduced Exploitable Risk – By validating threats, CTEM ensures resources are spent on risks that attackers can realistically exploit.
- Efficient Resource Allocation – Teams focus their remediation efforts on the vulnerabilities with the highest business impact.
- Lower Operational Costs – Automation and prioritization reduce wasted time and costs associated with manual risk management.
- Increased Organizational Resilience – Continuous exposure management helps organizations sustain operations even in the face of sophisticated cyberattacks.
CTEM vs. Traditional Vulnerability Management
Best Practices for Implementing CTEM in Cybersecurity
- Establish Clear Objectives – Define the purpose of CTEM within the organization, focusing on reducing exploitable risk.
- Adopt a Risk-Based Approach – Use business context, asset criticality, and exploit likelihood to guide prioritization.
- Integrate Threat Intelligence – Enrich exposure management with global and industry-specific threat feeds for contextual insights.
- Leverage Automation and AI – Utilize automated vulnerability discovery, AI-driven analytics, and orchestration platforms such as VerifiedThreat to improve efficiency.
- Promote Cross-Functional Collaboration – Foster cooperation between IT, security, compliance, and executive teams to ensure remediation is carried out effectively.
- Measure and Report Outcomes – Track metrics such as mean time to remediation (MTTR), reduction in high-risk exposures, and improved compliance alignment.
Future of CTEM in Cybersecurity
The adoption of CTEM will accelerate as organizations seek stronger, more adaptive defenses. Emerging trends shaping the future include:
- AI-Enhanced Prioritization: Leveraging machine learning to predict which vulnerabilities are most likely to be exploited.
- Integration with Zero Trust Architectures: CTEM complements Zero Trust by continuously validating user, device, and application security.
- Cloud-Native CTEM Platforms: Purpose-built tools for securing multi-cloud and hybrid environments.
- Automated Remediation Workflows: Seamless remediation through security orchestration, automation, and response (SOAR) platforms.
Organizations that adopt CTEM early will gain a competitive edge by strengthening security posture, ensuring compliance, and maintaining customer trust.

.svg)
.svg)
.svg)